Static analysis tools scan your code before deployment. Vulnerability scanners check your dependencies against CVE databases. Perimeter firewalls inspect incoming HTTP traffic. All of these are valuable, and all of them share the same blind spot: none of them can tell you what is actually happening inside your application right now.
Runtime threat detection fills that gap. It monitors applications, workloads, and services during execution, identifying and responding to attacks as they happen. Instead of predicting what might be vulnerable, it observes what is actually being exploited.
This article covers what runtime threat detection is, the three core detection strategies it uses, how it compares to traditional security tools like IDS and WAF, and how modern approaches bring detection capabilities directly into application code.
What Is Runtime Threat Detection?
Runtime threat detection is the process of monitoring applications and systems during execution to identify, classify, and respond to security threats in real time. Unlike static analysis or pre-deployment scanning, runtime detection operates on live behavior, observing how data flows through code, what processes execute, and which external connections are made while the application is actively serving traffic.
Its scope extends across the technology stack. Container orchestrators like Kubernetes use runtime detection to catch container escapes and privilege escalation. Cloud platforms use it to flag unauthorized API calls and resource access. And at the application layer, runtime detection intercepts injection attacks, command execution, and increasingly, LLM prompt manipulation before they cause damage.
What makes this approach fundamentally different from pre-deployment security is the quality of signal. A SAST tool might flag a potential SQL injection based on a code pattern. Runtime detection sees the actual malicious SQL statement reaching your database driver. That distinction matters. False positives drop significantly when you can verify that an attack is real, not theoretical.
The tradeoff is timing. Static tools catch vulnerabilities when they are cheapest to fix, during development. Runtime detection catches exploitation when it is most dangerous, in production. The most effective security strategies use both: static analysis tools scanning code in CI pipelines, and runtime security solutions monitoring behavior in production. Neither replaces the other. They cover fundamentally different phases of the application lifecycle.
How Runtime Threat Detection Works
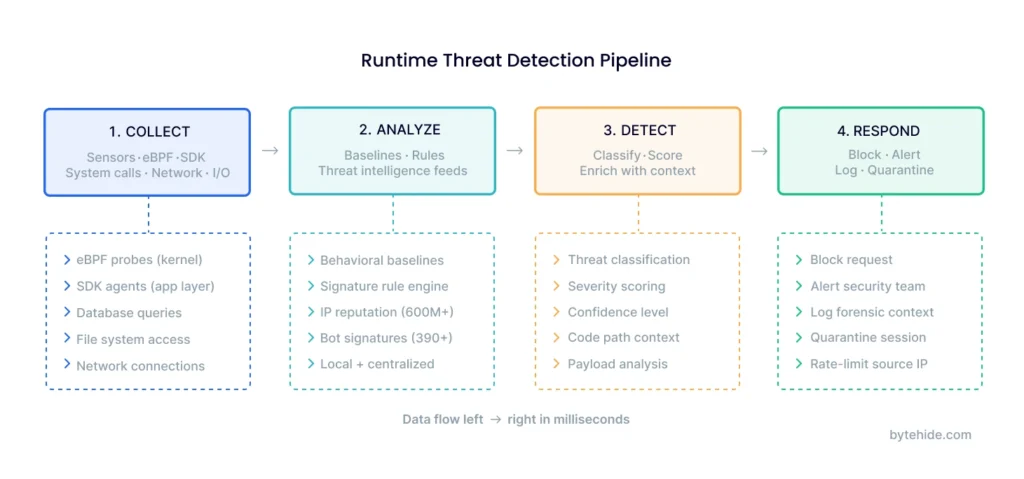
The detection process follows a four-stage pipeline: collect, analyze, detect, and respond. Understanding each stage helps clarify why some tools catch threats that others miss, and why real-time threat detection requires more than just monitoring network traffic.
Collection is where sensors gather raw runtime data. What gets collected depends on the detection layer. At the infrastructure level, eBPF probes capture system calls, network connections, and process executions from the kernel. At the application level, lightweight SDKs or agents intercept specific operations: database queries, file system access, OS command execution, template rendering, and outbound HTTP requests. The quality of collection determines the ceiling for everything downstream. Sensors that only see network packets will never catch an injection attack that reaches a database driver through a legitimate-looking HTTP request.
Analysis engines process collected events against baselines, rules, and threat intelligence feeds. This is where the three detection strategies (covered in the next section) come into play. Analysis can happen locally within the application process for latency-sensitive decisions, or it can happen in a centralized platform for correlation across multiple services.
Detection is the classification step. The analysis engine determines whether an event represents a genuine threat, assigns a severity level and confidence score, and enriches the finding with context: what code path was involved, what the attacker’s payload looked like, which user session triggered it, and what the potential impact would be if the attack succeeded.
Response is the action taken once a threat is confirmed. Automated responses include blocking the malicious request, terminating the compromised session, rate-limiting the source IP, and logging full forensic context for investigation. The response should match the confidence level. High-confidence detections (a confirmed SQL injection reaching a database query) can be blocked immediately. Lower-confidence anomalies might trigger alerts without blocking, giving security teams the information they need to investigate.
Three Core Detection Strategies
Most content about runtime detection focuses exclusively on anomaly detection. In practice, effective runtime threat detection combines three distinct strategies, each with different strengths and tradeoffs.
Anomaly Detection (Behavioral Analysis)
Anomaly detection works by establishing a baseline of normal behavior and flagging deviations. During a learning phase, the detection system records what “normal” looks like for each application: which processes it spawns, what network connections it makes, which files it accesses, what system calls it uses.
Once the baseline is established, real-time threat detection kicks in: the system compares live behavior against the baseline continuously. A web server that suddenly spawns a shell process is anomalous. A container accessing files outside its expected scope is anomalous. A database client making outbound HTTP requests to an unknown IP is anomalous.
Where anomaly detection excels is coverage against unknown threats. Because it does not rely on signatures, it can catch zero-day exploits, novel attack techniques, and supply chain compromises that no rule database has cataloged yet. The MITRE ATT&CK framework documents hundreds of attack techniques, and new ones emerge regularly; anomaly detection handles them without signature updates.
But there is a limitation: the learning period. Until the baseline is established, the system either misses threats (if too permissive) or generates excessive alerts (if too strict). Noisy environments with frequent deployments require longer or more sophisticated baselining.
Rule-Based Detection (Signature Matching)
Rule-based detection matches runtime events against pre-defined patterns of known attacks. When a SQL query contains OR 1=1, when a system command includes pipe redirections to a remote IP, when an HTTP request carries a path traversal sequence like ../../etc/passwd, rule engines catch these patterns immediately.
This strategy provides instant protection with very low false positive rates for known attack types. A well-tuned rule that matches SQL injection syntax in a database query is almost never wrong. Modern In-App WAF solutions cover multiple attack categories with dedicated interceptors: SQL injection, NoSQL injection, XSS, path traversal, command injection, SSRF, LDAP injection, XXE, and even LLM prompt injection.
The limitation is obvious: rule-based detection only catches what it has rules for. Novel encodings, fragmented payloads, and attack techniques that don’t match existing signatures will bypass it. That is why rule-based detection works best in combination with the other two strategies.
Threat Intelligence Integration
Threat intelligence integration cross-references runtime events against external databases of known malicious actors, IP addresses, bot signatures, and attack infrastructure.
When a request arrives from an IP address flagged across multiple threat intelligence feeds, the detection system can block or scrutinize that request before any application code processes it. This is preemptive detection: stopping known bad actors at the door rather than waiting to see if they attempt an exploit. Modern runtime detection platforms aggregate data from multiple sources. ByteHide Monitor, for example, integrates 7 threat intelligence lists covering 600 million known malicious IPs and maintains a database of 390+ bot user agents across 21 categories.
Where threat intelligence excels is immediacy. There is no learning phase and no signature-matching latency. If an IP address has been involved in attacks against other organizations, you benefit from that collective knowledge immediately.
The limitation is that threat intelligence is inherently retrospective. A brand-new attacker using a fresh IP address with no history will bypass reputation checks. That is why it works as a first filter combined with deeper behavioral and rule-based analysis for the traffic that gets through.
| Strategy | Catches | Misses | Speed | False Positive Rate |
|---|---|---|---|---|
| Anomaly Detection | Zero-days, novel attacks, behavioral shifts | Attacks during learning phase | After baseline | Medium (initially) |
| Rule-Based | Known injection, XSS, traversal, command exec | Novel encodings, new techniques | Immediate | Very low |
| Threat Intelligence | Known malicious IPs, bots, attack infrastructure | New/unknown attackers | Immediate | Very low |
In my experience, teams that rely on a single strategy always have gaps. Anomaly detection alone generates too many alerts in dynamic environments. Rules alone miss novel attacks. Threat intel alone misses attackers using clean infrastructure. Layering all three is what makes runtime detection reliable.
Runtime Threat Detection vs Traditional Security
Runtime threat detection at the application layer occupies a unique position in the security stack. Understanding how it differs from traditional tools helps clarify where each fits.
| Dimension | IDS/IPS | Perimeter WAF | EDR/XDR | Runtime Threat Detection (App-Layer) |
|---|---|---|---|---|
| Layer | Network | Network perimeter | Endpoint / OS | Application code |
| Visibility | Packets, flows | HTTP requests, headers | Files, processes, registry | Data flow, queries, commands, LLM prompts |
| Context | IP/port level | URL/header level | Process level | Code execution level |
| False positives | Medium-high | Medium | Medium | Low (sees execution context) |
| Zero-day detection | Limited (signature-based) | Limited (rule-based) | Yes (behavioral) | Yes (behavioral + code context) |
| Deployment | Network tap or inline | Reverse proxy / CDN | Agent on endpoint | SDK inside application |
The key difference is context depth. A perimeter WAF sees that a request parameter contains: OR 1=1--. It does not know whether that string will actually reach a SQL query, or whether the application sanitizes it somewhere in the processing chain. Application-layer runtime detection sees the exact SQL statement that reaches the database driver. It confirms whether the injection is real, not theoretical.
This context is why application-layer detection has significantly lower false positive rates. It does not need to guess whether an input is dangerous; it waits until the input is about to do something dangerous, and intercepts at that point.
That said, application-layer detection does not replace perimeter security. WAFs remain valuable for filtering high-volume bot traffic and blocking obvious attacks before they consume application resources. IDS/IPS still matters for network-level visibility. EDR protects endpoints from malware. Each tool covers a different layer, and defense in depth requires all of them.
Runtime Threat Detection for Applications
Most existing content on this topic focuses on containers and Kubernetes. Container-level detection using eBPF to monitor system calls across orchestrated workloads is important, but it operates at the infrastructure layer. It sees processes and system calls. It does not see how user input flows through your Express routes into a Sequelize query.
Application-layer detection works differently. Instead of monitoring infrastructure, it embeds inside the application and intercepts specific security-critical operations: database queries before they execute, OS commands before they spawn, file operations before they complete, and LLM prompts before they reach the model.
This approach is particularly relevant for teams building web applications, APIs, and services where the attack surface is the application code itself. If an attacker sends a SQL injection payload, application-layer detection does not just see the HTTP request. It sees the payload reaching the actual db.query() call, with full context about the method, the payload content, and the confidence that this is a real attack.
Here is what adding runtime threat detection to an application looks like in practice:
// Node.js — Add runtime threat detection in 3 lines
const monitor = require('@bytehide/monitor');
monitor.init({ apiKey: 'your-api-key' });
app.use(monitor.protect());
// Monitor now intercepts at 9 security-critical points:
// - SQL queries before db.query() executes
// - OS commands before child_process.exec() runs
// - File operations before fs calls complete
// - LLM prompts before they reach the model
// - XSS payloads, SSRF attempts, path traversal, LDAP injection, XXE// .NET — Equivalent setup
using ByteHide.Monitor;
var builder = WebApplication.CreateBuilder(args);
builder.Services.AddByteHideMonitor(options => {
options.ApiKey = "your-api-key";
});
var app = builder.Build();
app.UseByteHideMonitor(); // Runtime threat detection activeThis also covers serverless functions and cloud-native architectures. Because detection embeds as an SDK rather than requiring infrastructure agents, it works in AWS Lambda, Azure Functions, and other environments where you do not control the underlying host. That makes it the practical option for runtime threat detection across serverless functions and traditional deployments alike.
One capability worth highlighting: LLM prompt injection detection. As organizations integrate language models into their applications, a new category of runtime threats has emerged. Jailbreak attempts, system prompt extraction, role manipulation, and encoded payloads all target the model during inference, a purely runtime event. Application-layer runtime detection intercepts prompts before they reach the model, matching against known injection patterns. This addresses OWASP’s top risk for LLM applications at the execution point.
Best Practices for Runtime Threat Detection
Start in detection mode before enabling blocking. Deploy runtime detection in alert-only mode first. This lets you establish baselines, tune detection thresholds, and understand your application’s normal behavior before automated blocking potentially interrupts legitimate traffic. Most teams run in detection mode for one to two weeks before switching to active blocking.
Layer all three detection strategies. Anomaly detection catches unknown threats. Rule-based detection catches known attacks with very low false positives. Threat intelligence blocks known bad actors preemptively. Use all three. No single strategy covers everything.
Combine static analysis with runtime detection. SAST tools find vulnerabilities in code during development. Runtime detection catches exploitation in production. When the two share data, the loop closes: runtime detection confirms which SAST findings are actively being exploited, which lets your team reprioritize from “medium” to “critical” based on real-world evidence rather than theoretical risk scores. Platforms like ByteHide that integrate both static analysis (Radar) and runtime protection (Monitor) can automate this feedback loop.
Automate incident response. When detection confirms a high-confidence threat, the response should be automatic: block the request, log forensic context (payload, code path, confidence score, session data), and alert the security team. Manual response is too slow for attacks that execute in milliseconds.
Monitor AI and LLM integrations. If your application calls language models, treat those prompts as security-sensitive operations. Apply runtime detection at the inference boundary. This is a growing attack surface that most security stacks do not cover yet.
Feed runtime data back to development. Runtime threat detection is not just a production defense. The data it generates, which vulnerabilities are being targeted, which attack vectors are most common, what payloads attackers are using, is invaluable intelligence for development teams prioritizing what to fix next.
Frequently Asked Questions
What is runtime threat detection?
Runtime threat detection is the process of monitoring applications and systems during active execution to identify and respond to security threats in real time. It uses three core strategies: anomaly detection (behavioral baselining), rule-based detection (signature matching against known attack patterns), and threat intelligence integration (cross-referencing events against databases of known malicious actors). Unlike static analysis, which evaluates code at rest, runtime detection observes live behavior and can confirm whether an attack is real, not just theoretically possible.
What are the four types of threat detection?
The four main types of threat detection are signature-based detection (matching known attack patterns), anomaly-based detection (identifying deviations from normal behavior), behavioral analysis (monitoring entity actions over time for suspicious patterns), and threat intelligence-based detection (cross-referencing activity against external feeds of known threats). In runtime contexts, these are often combined. For example, application-layer runtime detection uses rule matching for known injections, anomaly detection for novel attacks, and IP reputation data to filter known malicious traffic simultaneously.
How does runtime threat detection differ from static analysis?
Static analysis (SAST) examines source code without executing it, identifying potential vulnerabilities based on code patterns during development. Runtime threat detection monitors the application during execution, identifying actual attacks as they happen in production. Static analysis finds where vulnerabilities exist in your code. Runtime detection tells you when someone is exploiting them. Most security teams use both: static analysis to fix vulnerabilities early, runtime detection to block exploitation of anything that reaches production.
Can runtime threat detection protect against zero-day attacks?
Yes. Anomaly-based runtime detection identifies zero-day attacks by detecting unusual behavior that results from exploitation, even when the specific vulnerability is unknown. A zero-day exploit still produces observable effects: unexpected process spawning, unauthorized file access, abnormal network connections, or SQL queries with injected payloads. Runtime detection catches these behavioral indicators regardless of whether the vulnerability has been cataloged in any database.
Do I need runtime threat detection if I already have a WAF?
A perimeter WAF filters HTTP traffic based on request patterns, but it operates without application context. It cannot verify whether a suspicious input actually reaches a vulnerable code path inside your application. Runtime threat detection at the application layer confirms real exploitation by intercepting threats at the execution point, where the data actually interacts with database queries, system commands, or file operations. The two are complementary: a WAF reduces noise by filtering obvious attacks at the perimeter, while runtime detection catches sophisticated attacks that bypass WAF rules.
Runtime threat detection is no longer a nice-to-have for organizations running production applications. Whether your stack runs on Kubernetes, serverless functions, or traditional servers, threats that target running code require detection that operates at runtime. If you want to see how application-layer runtime threat detection works in practice, explore ByteHide Monitor.





